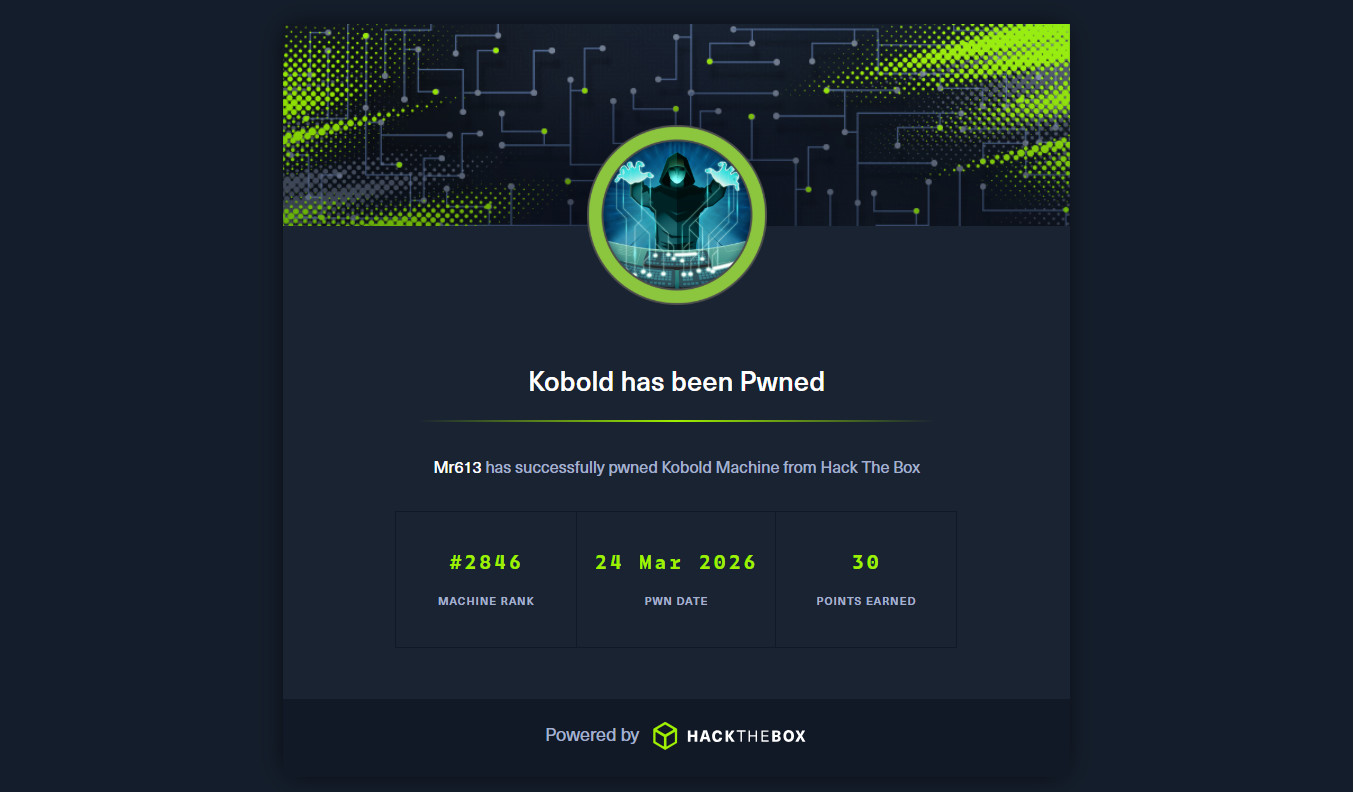
"kobold" - HackTheBox Walkthrough (Season 10)
Step by step walkthrough of the Kobold HTB machine. this writeup covers unauthenticated RCE in MCPJam Inspector and privilege escalation via Docker group abuse.
HackTheBox “kobold” Writeup
A walkthrough of the HackTheBox Kobold machine (Season 10), an Easy rated Linux box. we will coverinitial access through a CVE in an MCP dev tool and then privesc through a classic docker group escape.
- Before we get into it; i know, another easy box. and yeah, it’s been a while since my last writeup.
- I’ve been kinda busy lately, a bunch of stuff all hit at the same time. i’m still hacking weekly when machines drop, just haven’t had the bandwidth to sit down and write everything up properly.
- kobold was worth writing up specifically because the CVE touches on MCP tooling which is super relevant right now with the whole AI agent ecosystem blowing up. felt like something worth documenting even if the box itself is rated easy. Wish i had more time to do harder machines.
Initial Recon
standard nmap first, given machine IP is 10.129.72.174:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
┌──(kali㉿kali)-[~/Desktop]
└─$ nmap -A -T5 10.129.72.174 -p-
Nmap scan report for kobold.htb (10.129.72.174)
Host is up (0.063s latency).
Not shown: 65486 closed tcp ports (reset), 45 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.15 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 8c:45:12:36:03:61:de:0f:0b:2b:c3:9b:2a:92:59:a1 (ECDSA)
|_ 256 d2:3c:bf:ed:55:4a:52:13:b5:34:d2:fb:8f:e4:93:bd (ED25519)
80/tcp open http nginx 1.24.0 (Ubuntu)
|_http-title: Did not follow redirect to https://kobold.htb/
|_http-server-header: nginx/1.24.0 (Ubuntu)
443/tcp open ssl/http nginx 1.24.0 (Ubuntu)
|_http-title: Kobold Operations Suite
| ssl-cert: Subject: commonName=kobold.htb
| Subject Alternative Name: DNS:kobold.htb, DNS:*.kobold.htb
| Not valid before: 2026-03-15T15:08:55
|_Not valid after: 2125-02-19T15:08:55
|_http-server-header: nginx/1.24.0 (Ubuntu)
3552/tcp open http Golang net/http server
|_http-title: Site doesnt have a title (text/html; charset=utf-8).
three notable ports to investigate:
- port 80 : just redirects to HTTPS, nothing there
- port 443 : the TLS cert has
DNS:*.kobold.htb, as expected there will probably be subdomains to find - port 3552 : Go HTTP server, nmap can’t really fingerprint it
added it to /etc/hosts:
1
2
3
┌──(kali㉿kali)-[/home/kali/Desktop/kali_shared]
└─$ echo "10.129.72.174 kobold.htb" | sudo tee -a /etc/hosts
10.129.72.174 kobold.htb
Active HackTheBox Challenge
This challenge is currently active on HackTheBox. According to HTB's content policy, sharing writeups of active challenges is prohibited.
This writeup will be made publicly available once the challenge is retired. If you wish to know the password or discuss the challenge, please reach out via the social links below.
Conclusion
quick, fun box. the initial foothold through mcpJam was kinda cool, mcp is everywhere with the whole ai boom and a lot of these dev/debug platforms might have a similar fate. the privesc was a standard docker group escape but the extra stepswith --entrypoint and --user root made it less copypasta.
How It Can Be Prevented
a few things this box got badly wrong that are genuinely easy to fix:
bind to localhost, not 0.0.0.0
add auth to important API endpoints
never add regular users to the docker group
don’t leave dev tooling running in production